HACK Issue 006: Web3 Security resources, Drivers vs Passengers, and Security Leaders need to be Salespeople
TGIF ya'll. I hope your week has been a good one and you're heading strong into the weekend.
Onwards...
Security tweets and links
Life is to short to use dated cli tools that suck. Use these tools instead. List curated by @amilajack.
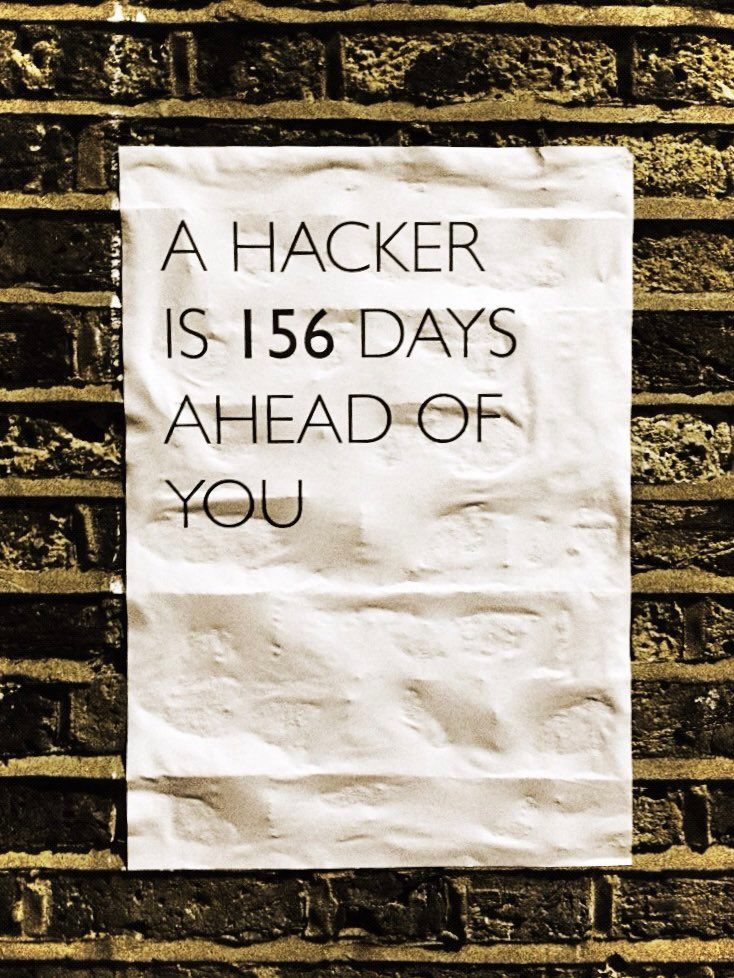
This popped back up into my stream this week. Avg time from penetration to breach discovery: 156 days. That was circa 2014, wonder if it's changed since?
web3 security resources: tools, ctfs, writeups. Nice repo.
If you say "“privileged access to any resource in AWS”, you better be damn sure. I may or may not have subtweeted on this as well 🤐. I mean kudos to Free Willy on the finds, but if you're gonna post about the sexy vuln, gotta include the technical goods imho.
Posted without comment: Shawty, we're gonna do bug bounties
Marketing thought of the week: A message to security leaders
Thesis: Security leaders need sales skills to be successful.
What is the biggest challenge of security leaders? Is it understanding and cataloguing your growing attack surface? Getting employees not to click on that Phishing email? Patching?
The biggest challenge I see is convincing other leaders in your company about what security is, why it's a shared responsibility, and why they must invest in it with you.
You need to learn to be a salesperson.
Soft skills. Persuasion techniques. Charm and grace. Positive attitude. Put that sleazy ambulance chasing salesperson out of your mind right now and embrace the power of persuasive conversation, artfully crafted pitches, perfectly timed comments, expertly prepared research, compelling data, and a winning mindset.
At HackerOne I helped produce almost 30 live hacking events over 5-years for almost 20 customers including Goldman Sachs, Yahoo, Dropbox, Airbnb, Uber, Shopify, Mapbox, and The US Department of Defense.
Do you think those leaders got approval to spend between $500K - $1M without having a compelling narrative?
I would call this skill: bureaucracy hacking. A combination of social engineering (that's what sales and marketing is at the end of the day that's why it must be done with integrity) and political acumen and tenacity.
And as a marketer looking to get the attention of DevOps, SecOps, and Directors of Security, it is in my best interest to equip my readers and target audience with the right story, the right value, the right data to be able to talk to internal stakeholders like legal, procurement, C-suite personas, and more. Look for more to come on this topic from me. I think a lot of this is about building a culture of security and privacy and your company as well. One of my favorite presentations ever done in regards to that topic was Arkadiy Tetelman at BSides SF in 2019. Check it out:
Inspirational note: Drivers vs Passengers
The Snowflake CEO has a new book coming out soon. Jason Calacanis said on a recent All in Podcast that it was a must read. Frank posted some excerpts in a LinkedIn post, which I included below:
I still ask myself this question at the end of each week: what did I do this week that moved the dial, how instrumental and essential was I this week? In the privacy of your own mind, it is hard to BS yourself. Is the answer equally good every week? No, and that is the point of the exercise. Hold yourself to a higher standard.
Hold yourself to a higher standard. Love that. But also, don't be afraid to be transparent when you mess up. I recently connected with a friend this week who shared a blog post with me about some of their personal journey with addiction, mental health challenges and more. I was so encouraged by the duality of these two posts. One is about striving to be your best each week and holding yourself to a higher standard, and the other is about "you know what, I'm going to mess up. Not if but when. Let me have grace with myself and make sure I don't be so hard on myself. Pick myself back up and stay consistent. Progress, not perfection."
Push yourself to be your best but offer grace to yourself and others. Empathy is a superpower.
Until next week friends,
L
