Jonathan Scott's end game and my advice for infosec twitter and jonathandata1
Jonathan Scott is smart. He doesn’t care what the security community thinks, but he does care about what the general population thinks. Let’s track his journey a bit to postulate the end game. Now, every step he's taken could be completely natural and passion-driven, I have no idea. I think Jonathan genuinely believes his claims at his core. Stick around to the end for my advice for infosec twitter and for Jonathan.
Act 1: America’s #1 hacker
Act 1, part 1: Leveraging the HackerOne reputation system to claim the position as a “top US hacker” because he was publicly listed on the Department of Defense's vulnerability disclosure program leaderboard. He submitted around 600 reports and every valid VDP report gets awarded +7 reputation, more than enough to reach a quarterly leaderboard top position. A few Nessus scans later and a few hundred p5 submissions, you get yourself a branding feather in the cap without much effort. This is not respected or sought after by the core bug bounty or infosec community, but that's not the target audience.
Act 1, part 2: Jonathan starts streaming on YouTube how he found information in government sites. Around that time, he got banned from pretty much every major bug bounty platform for disclosing PII among other code of conduct violations. No matter, it’s all part of the plan. Infamy over innocence.
Act 1, part 3: He livestreams and tweets about mobile vulnerabilities, mobile malware and spyware. Now it could be he just loves this corner of security - awesome! It also is smart from a marketing perspective. Here's why: because everyone has a cell phone. “This is a big deal” people will think. He’s now branching out to hit a broader audience. Obscure DoD sites are vulnerable? Darn government, don’t trust em. But when there’s security issues in the phone that you’re holding in your hand - now it’s personal, now it hits close to home. Im vulnerable, and so is the government! Yikes!
These are the types of videos that get innocently shared with grandmas and uncles throughout social media evangelizing the dangers of technology, corruption and carelessness of big tech, and more. It’s the type of content that the social platforms eat up like syrup on pancakes.
Act 2: Evolving to an international stage: Beijing Olympics mobile app controversy
This is tailor made for Jonathan's strategy. The Olympics are one of the largest events loved and watched around the world… USA's biggest competitive rivals in the Olympics include Russia and China, same on the geopolitical stage (ahem, Ukraine).
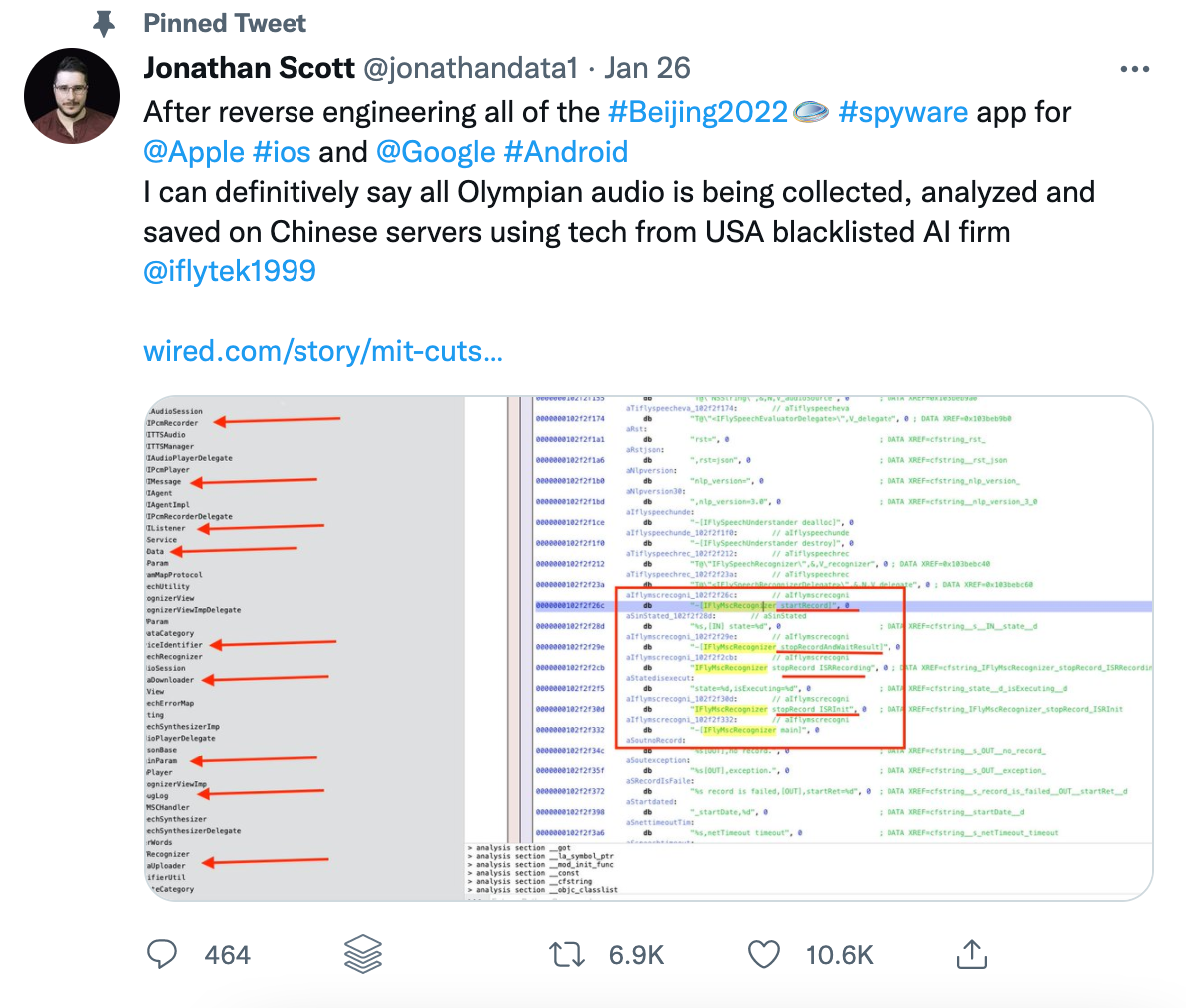
USA: what says more about national pride and being an American hero than disclosing how American athletes are being tracked and forced to download an app exposing their location, conversations and more. One note on this, I think everyone agrees that the app is sketchy, however, no one really agrees on all of Jonathan's technical claims including Google Project Zero's @taviso, CTFer and YouTuber cts, experienced journalist Dan Goodin and many more.
The Olympics are in Beijing, China. China, especially in conservative circles of the USA, are lambasted for coronavirus, communism, censoring and spying. All kinds of kindling for a scandal.
With Act 1 fully complete, Act 2 slingshots him into a new threshold. Who’s who of security journalists and hackers calling him out on one side. Washington Post journalists tweeting to the White House, BBC producers inviting him on their show on the other side. This gets more in the realm of misinformation (if untrue claims are made) and regardless it provides international intrigue, a whole different level indeed.
Act 3: Capitalize or dissipate
I’m not sure how much Jonathan pre-planned his infamy and I don’t exactly know how this will all play out. It either will be successful and vault him into elevated influence or flame out. Who knows.... I do have some theories below as to how Act 3 could go. Perhaps next up is a mobile app tech scandal related to Russia and Ukraine? Overall, eventually he'll want to capitalize on the fame in a bigger way through political achievement or economic achievement. Potential next steps for jonathandata1:
- Pivot his podcast to injustices beyond the hacking scene. Like Joe Rogan, but technical
- Write a book: a human interest story and "BTS" or "Making of" a hacker hero type of thing.
- Launch a security consultancy or tool or course
- Run for political office
- Do a combination of one or two or all of the above
A note to infosec twitter and to Jonathan
Jonathandata1 is an example of how anyone remotely technical with the right recipe can gain notoriety by feeding on the right populist trends, engaging in twitter spats and throwing out big technical claims which spread like wildfire in today's social media landscape.
So how to handle this?
One option is to ignore. He’s built a profile based on controversy. Angry subtweets, YouTube videos et al are oxygen to his machine. But I don’t think that’s realistic to ignore across the board. We’re too social, we’re too addicted to our itchy finger tweeting that we can’t be silent.
People who disagree feel compelled to speak up, and many times rightfully so. My advice to the infosec community is to take a different approach when calling out believed inaccuracies: empathy and coaching. Speaking the truth in love. Approach conversations with civility and curiosity. Ask clarifying questions. Creators, continue to create response material but focus on matter of fact articulate and logical responses. Come from a space of curiosity and when necessary submit kind but firm rebuttals. Ask which malware researchers he admires and looks up to. Where he gets his inspiration from. Reach out to journalists behind the scene who you believe are jumping the gun, help to educate them as well.
Jonathan, if you read this, you are talented. You’ve got a skill for marketing, use that gift with wisdom. Create value, not controversy. Fame is fickle. Stay humble but hungry. Build a firm foundation not based on sensationalism, but honesty and truth. Seek first to understand, not just be understood. Prioritize discourse and conversation over likes, clicks, and comments. I think you'll find if you do that, your long term fame and economic outlook is vastly better than the current track.
As I write the above advice, I realize it's wisdom I too can be reminded of and challenged by. No one's perfect, and real leaders are always learning and growing. Let's try and spend more time celebrating great security work like samcszun and team reverse engineering the wormholecrypto exploit, cool research into AWS EMR like Lightspin researcher Dana, or any number of the recently disclosed issues on HackerOne's hacktivity.
